Introduction to Image Steganography
In the digital era, protecting information has become just as important as sharing it. One subtle and effective way to safeguard data is image steganography, a technique that conceals secret information inside digital images. Unlike encryption, which scrambles data into unreadable formats, steganography hides information in plain sight. Among the many approaches developed in this field, pixel value differencing stands out for its balance of security, simplicity, and efficiency. This method leverages the natural variations between neighboring pixels to embed data without noticeably altering image quality, making it especially useful for secure communication over public networks.
How Pixel-Based Data Hiding Works
Understanding Pixel Relationships
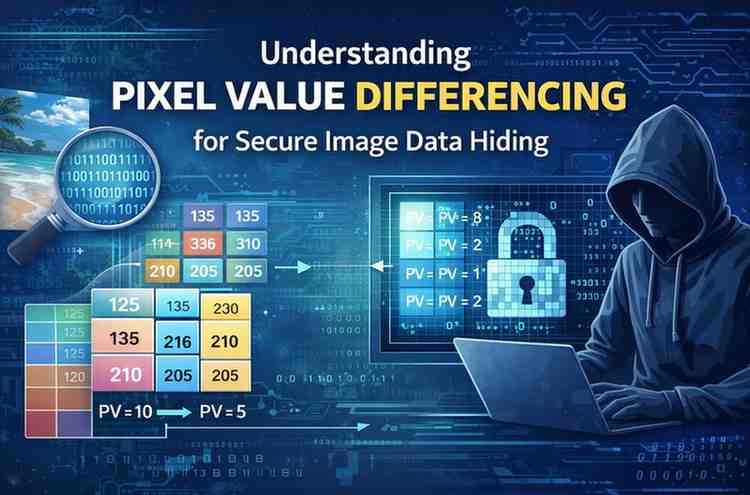
Digital images are made up of pixels, each representing an intensity value in grayscale images or color components in RGB images. Human vision is less sensitive to changes in complex or high-contrast regions of an image. This insight forms the foundation of pixel value differencing, where the difference between adjacent pixel values determines how much data can be embedded.
Embedding Secret Information
When two neighboring pixels have a small difference, the area is smooth, and only a small amount of data is hidden. Larger differences indicate edges or textured regions, allowing more bits to be embedded safely. This adaptive approach ensures that hidden data remains invisible to the naked eye while maximizing embedding capacity.
Advantages of Adaptive Steganography Methods
Improved Image Quality
One major benefit of adaptive techniques is their ability to preserve visual quality. By adjusting data embedding based on pixel variation, distortion is minimized. Metrics like Peak Signal-to-Noise Ratio (PSNR) and Mean Squared Error (MSE) are often used to evaluate how closely the modified image matches the original.
Higher Security Levels
Compared to basic least significant bit methods, pixel value differencing offers stronger resistance to visual and statistical attacks. Since data is distributed according to image content, detecting hidden information becomes significantly more difficult, enhancing overall security.
Applications in Real-World Scenarios
Secure Communication
This technique is widely used for confidential data transmission. Sensitive messages can be hidden within ordinary images shared عبر email or social media, reducing suspicion and interception risks.
Medical and Legal Imaging
In healthcare and legal systems, image integrity is critical. Embedding patient records or authentication codes directly into medical images ensures data consistency and helps prevent tampering without compromising diagnostic quality.
Digital Watermarking
Copyright protection is another key application. By embedding ownership information into images, creators can assert rights and track unauthorized usage while maintaining visual fidelity.
Challenges and Limitations
Despite its strengths, pixel value differencing is not without challenges. It is more complex to implement than simpler methods and requires careful calibration to avoid overflow or underflow in pixel values. Additionally, aggressive image processing operations like compression or resizing can damage hidden data. Researchers continue to explore hybrid models and machine learning enhancements to address these limitations and improve robustness.
FAQ
What is image steganography?
It is the practice of hiding secret data within digital media like images so that the presence of the data is concealed.
Is this technique noticeable to human eyes?
No, when implemented correctly, changes remain imperceptible.
Can hidden data be destroyed?
Yes, heavy compression or image editing can corrupt embedded information.
Is it better than encryption?
It serves a different purpose; steganography hides existence, while encryption hides meaning.
What types of images work best?
Grayscale and high-resolution images with varied textures are ideal.
Conclusion
Image steganography continues to evolve as digital communication grows. Among its many techniques, pixel value differencing remains a reliable and intelligent approach for secure data hiding. By exploiting natural pixel variations, it achieves an effective balance between invisibility, capacity, and security. While challenges exist, ongoing research and technological advances promise even more resilient and efficient methods in the future. For anyone interested in data protection, digital forensics, or multimedia security, understanding this technique offers valuable insight into the hidden layers of modern images.